The first cyber coverage to actively reduce risk
Comprehensive cyber insurance in a straightforward product. The best part? It can include cybersecurity solutions, software, and support to elevate your security to best-in-class.


The Elpha Difference
Leading Software
Our cybersecurity solution is designed with your cyber policy in mind, so we understand and see your risk from the very start.
Count on our Security Operations Center (SOC) for speedy support. Our SOC will respond to events in real time, which can help prevent and mitigate incidents and claims.
If you choose to use our security solution, you can get lower Retentions, Waiting Periods, and have longer Periods of Restoration to help you recover and get back to business quicker.



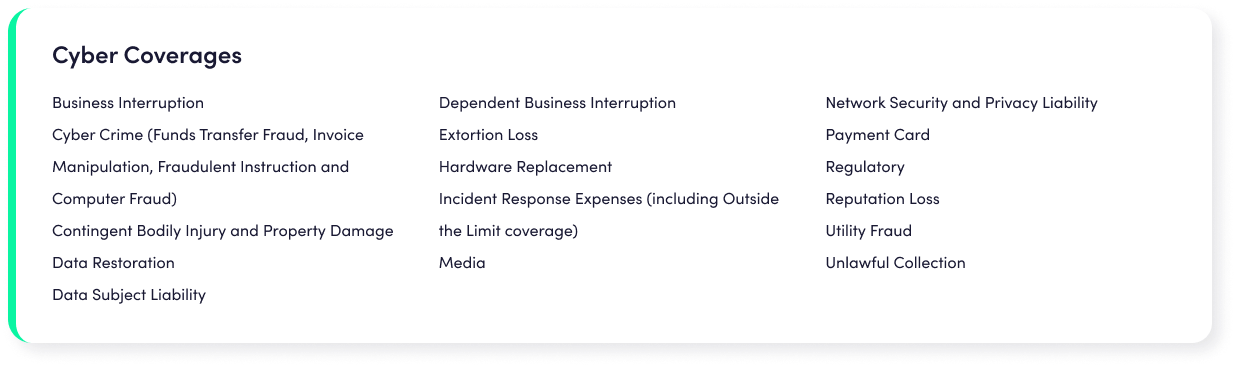
Cyber Insurance Coverage
From Ransomware to Business Interruption events, you can get comprehensive cyber insurance to help respond to your losses and security software to improve your cyber hygiene.
Elpha provides extensive cyber insurance coverage for your cyber risks plus software options to proactively mitigate cyber risk.
Our underwriting process is streamlined to deliver a quote on the spot.
We work with wholesale insurance brokers to deliver our product.
A cyberattack can happen to anyone. If it happens to you, we can help you land on your feet with a cyber policy that responds to serious threats.